A) Onguard Agent used
B) Authentication Method used
C) Network Access Device used
D) Active Directory Attributes
E) Endpoint OS Category
G) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 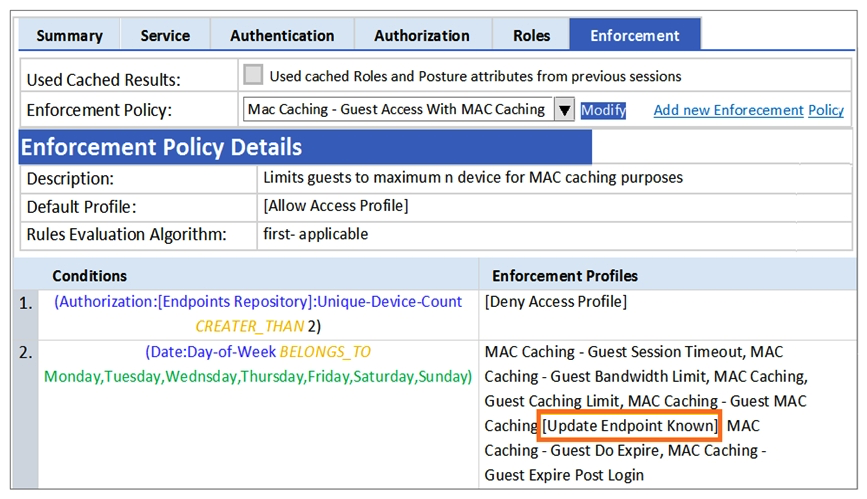 A guest to the Guest SSID and authenticates successfully using the guest php web login page. Based on the MAC Caching service information shown, which statement about the guest's MAC address is accurate?
A guest to the Guest SSID and authenticates successfully using the guest php web login page. Based on the MAC Caching service information shown, which statement about the guest's MAC address is accurate?
A) It will be visible in the Guest User Repository with Unknown Status.
B) It will be deleted from the Endpoints tables.
C) It will be visible in the Guest User Repository with Known Status.
D) It will be visible in the Endpoints table with Unknown Status.
E) It will be visible in the Endpoints table with Known Status.
G) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. ![Refer to the exhibit. An AD user's department attribute value is configured as Product Management . The user connects on Monday to a NAD that belongs to the Device Group HQ. Which role is assigned to the user in ClearPass? A) Linux User B) Executive C) [Employee] D) [Guest] E) HR Local](https://d2lvgg3v3hfg70.cloudfront.net/C1454/11ec574e_f89f_7c98_b2dd_699b8922921f_C1454_00.jpg) An AD user's department attribute value is configured as "Product Management". The user connects on Monday to a NAD that belongs to the Device Group HQ. Which role is assigned to the user in ClearPass?
An AD user's department attribute value is configured as "Product Management". The user connects on Monday to a NAD that belongs to the Device Group HQ. Which role is assigned to the user in ClearPass?
A) Linux User
B) Executive
C) [Employee]
D) [Guest]
E) HR Local
G) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A customer wants to implement Virtual IP redundancy, such that in case of a ClearPass server outage. 802.1x authentications will not be interrupted. The administrator has enabled a single Virtual IP address on two ClearPass servers. Which statement is true? (Choose two.)
A) Both the primary and secondary nodes will respond to authentication requests sent to the Virtual IP address when the primary node is active.
B) The primary node will respond to authentication requests sent to the Virtual IP address when the primary node is active.
C) The NAD should be configured with the primary node IP address for RADIUS authentications on the 802.1x network.
D) A new Virtual IP address should be created for each NAD.
E) The NAD should be configured with the virtual IP address for RADIUS authentications on the 802.1x network.
G) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 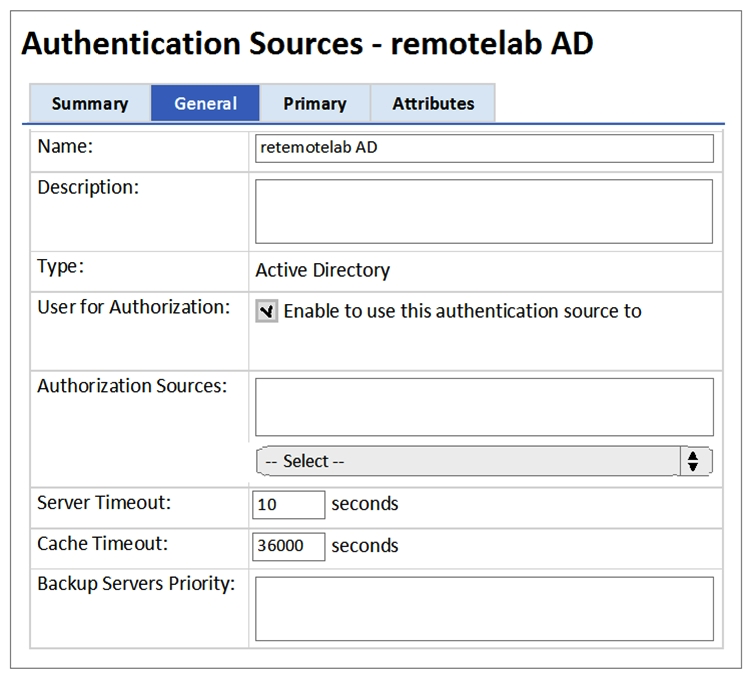 What does the Cache Timeout Value refer to?
What does the Cache Timeout Value refer to?
A) The amount of time the Policy Manager caches the user credentials stored in the Active Directory.
B) The amount of time the Policy Manager waits for a response from the Active Directory before checking the backup authentication source.
C) The amount of time the Policy Manager caches the user attributes fetched from Active Directory.
D) The amount of time the Policy Manager waits for response from the Active Directory before sending a timeout message to the Network Access Device.
E) The amount of time the Policy Manager caches the user\s client certificate.
G) A) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 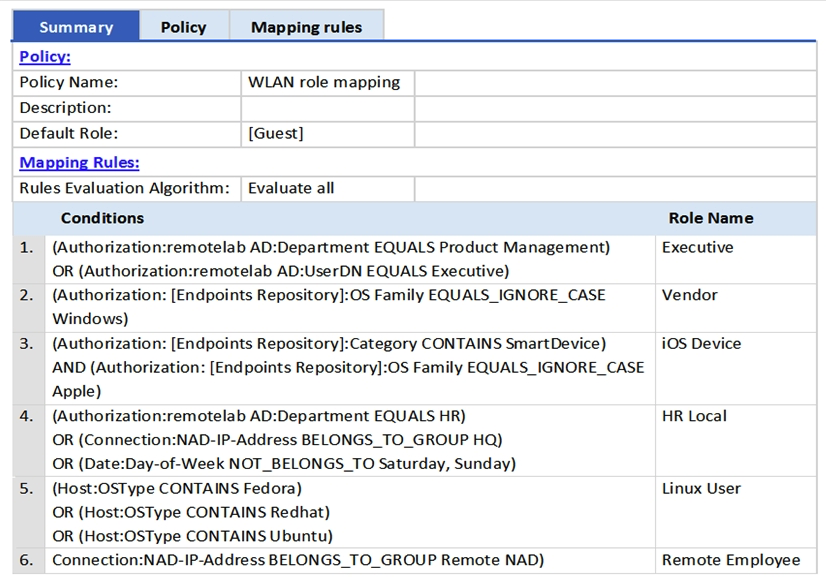 An AD user's department attribute is configured as "HR". The user connects on Monday using an Android phone to an Aruba Controller that belongs to the Device Group Remote NAD. Which roles are assigned to the user in ClearPass? (Choose two.)
An AD user's department attribute is configured as "HR". The user connects on Monday using an Android phone to an Aruba Controller that belongs to the Device Group Remote NAD. Which roles are assigned to the user in ClearPass? (Choose two.)
A) Remote Employee
B) Executive
C) Vendor
D) iOS Device
E) HR Local
G) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
What is RADIUS CoA (RFC 3576) used for?
A) To force the client to re-authenticate upon roaming to a new Controller.
B) To authenticate users or devices before granting them access to a network.
C) To validate a host address against a whitelist or a blacklist.
D) To transmit messages to the NAD/NAS to modify a user's session status.
E) To apply firewall policies based on authentication credentials.
G) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. ![Refer to the exhibit. Based on the information, what is the purpose of using [Time Source] for authorization? A) to check how long it has been since the last login authentication B) to check whether the guest account expired C) to check whether the MAC address is in the MAC Caching repository D) to check whether the MAC address status is known in the endpoints table E) to check whether the MAC address status is unknown in the endpoints table](https://d2lvgg3v3hfg70.cloudfront.net/C1454/11ec574e_f89e_9235_b2dd_cbf17c4c5f86_C1454_00.jpg) Based on the information, what is the purpose of using [Time Source] for authorization?
Based on the information, what is the purpose of using [Time Source] for authorization?
A) to check how long it has been since the last login authentication
B) to check whether the guest account expired
C) to check whether the MAC address is in the MAC Caching repository
D) to check whether the MAC address status is known in the endpoints table
E) to check whether the MAC address status is unknown in the endpoints table
G) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 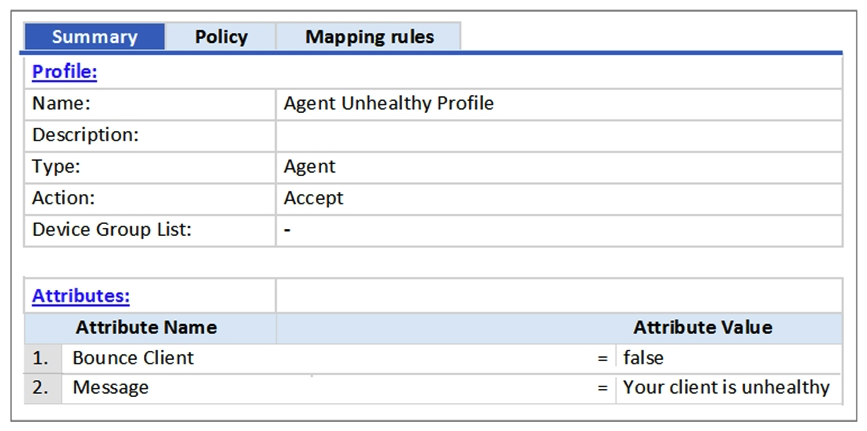 Based on the Enforcement Profile configuration shown, which statement accurately describes what is sent?
Based on the Enforcement Profile configuration shown, which statement accurately describes what is sent?
A) A limited access VLAN value is sent to the Network Access Device.
B) A message is sent to the Onguard Agent on the client device.
C) An unhealthy role value is sent to the Network Access Device.
D) A RADIUS CoA message is sent to bounce the client.
E) A RADIUS access-accept message is sent to the Controller.
G) A) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which checks are made with Onguard posture evaluation in ClearPass? (Choose three.)
A) Operating System version
B) Peer-to-peer application checks
C) EAP TLS certificate validity
D) Client role check
E) Registry keys
G) B) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 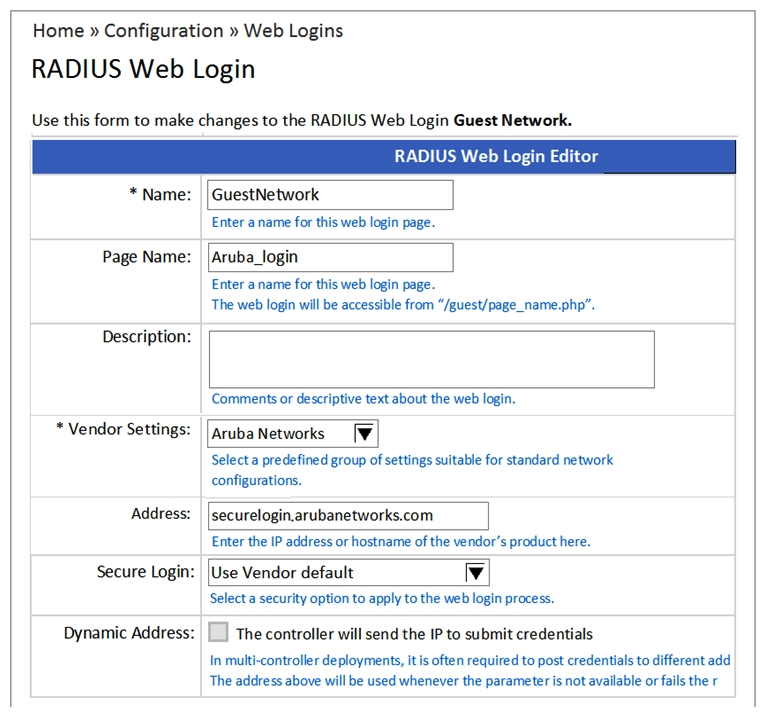 When configuring a Web Login Page in ClearPass Guest, the information shown is displayed. What is the Address field value 'securelogin.arubanetworks.com' used for?
When configuring a Web Login Page in ClearPass Guest, the information shown is displayed. What is the Address field value 'securelogin.arubanetworks.com' used for?
A) For the client to POST the user credentials to the NAD.
B) For ClearPass to send a RADIUS request to the NAD.
C) For ClearPass to send a TACACS+ request to the NAD.
D) For appending to the Web Login URL, after the page name.
E) For appending to the Web Login URL, before the page name.
G) A) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
What types of files are stored in the Local Shared Folders database in ClearPass? (Choose two.)
A) Backup Files
B) Posture dictionaries
C) Software image
D) Device fingerprint dictionaries
E) Log files
G) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which statement is true? (Choose two.)
A) Mobile device Management is the result of Onboarding.
B) Third party Mobile Device Management solutions can be integrated with ClearPass.
C) Mobile Device Management is the authentication that happens before Onboarding.
D) Mobile Device Management is an application container that is used to provision work applications.
E) Mobile Device Management is used to control device functions post-Onboarding.
G) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 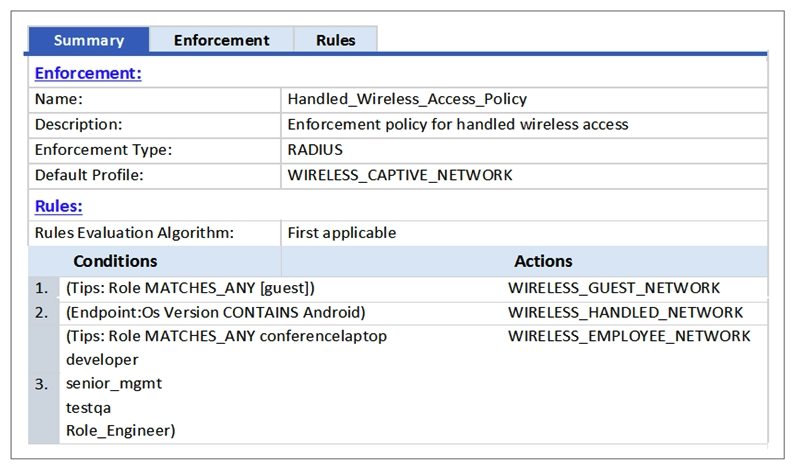 A user who is tagged with the ClearPass roles of Role_Engineer and developer, but not testqa, connects to the network with a corporate Windows laptop. Which Enforcement Profile is applied?
A user who is tagged with the ClearPass roles of Role_Engineer and developer, but not testqa, connects to the network with a corporate Windows laptop. Which Enforcement Profile is applied?
A) WIRELESS_GUEST_NETWORK
B) WIRELESS_CAPTIVE_NETWORK
C) WIRELESS_HANDHELD_NETWORK
D) WIRELESS_EMPLOYEE_NETWORK
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 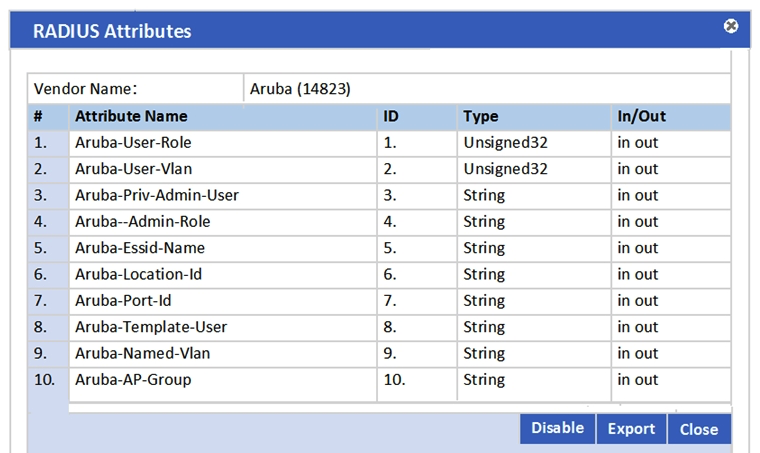 In the Aruba RADIUS dictionary shown, what is the purpose of the RADIUS attributes?
In the Aruba RADIUS dictionary shown, what is the purpose of the RADIUS attributes?
A) to send information via RADIUS packets to Aruba NADs
B) to gather and send Aruba NAD information to ClearPass
C) to send information via RADIUS packets to clients
D) to gather information about Aruba NADs for ClearPass
E) to send CoA packets from ClearPass to the Aruba NAD
G) None of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A customer wants to make enforcement decisions during 802.1x authentication based on a client's Onguard posture token. What enforcement profile should be used in the health check service?
A) Quarantine VLAN
B) RADIUS CoA
C) RADIUS Accept
D) RADIUS Reject
E) Full Access VLAN.
G) B) and E)
Correct Answer

verified
B
Correct Answer
verified
Multiple Choice
Refer to the exhibit. 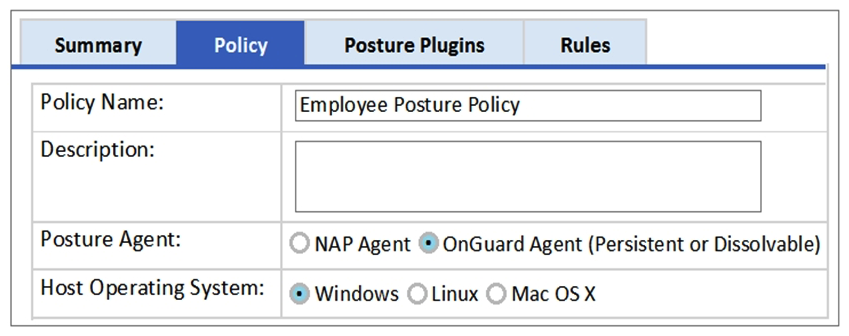 Based on the Posture Policy configuration shown, above, which statement is true?
Based on the Posture Policy configuration shown, above, which statement is true?
A) This Posture Policy can only be applied to an 802.1x wired service not 802.1x wireless.
B) This Posture Policy checks the health status of devices running Windows, Linux and Mac OS X.
C) This Posture Policy can use either the persistent or dissolvable Onguard agent to obtain the statement of health.
D) This Posture Policy checks for presence of a firewall application in Windows devices.
E) This Posture Policy checks with a Windows NPS server for posture tokens.
G) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
What must be configured to enable RADIUS authentication with ClearPass on a network access device (NAD) ? (Choose two.)
A) The ClearPass server must have the network device added as a valid NAD.
B) The ClearPass server certificate must be installed on the NAD.
C) A matching shared secret must be configured on both the ClearPass server and NAD.
D) An NTP server needs to be set on the NAD.
E) A bind username and bind password must be provided.
G) B) and E)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Which statement is true about the configuration of a generic LDAP server as an External Authentication server in ClearPass? (Choose three.)
A) Generic LDAP Browser can be used to search the Base DN.
B) An administrator can customize the selection of attributes fetched from an LDAP server.
C) The bind DN can be in the administrator@domain format.
D) A maximum of one generic LDAP server can be configured in ClearPass.
E) A LDAP Browser can be used to search the Base DN.
G) B) and D)
Correct Answer

verified
A,B,E
Correct Answer
verified
Multiple Choice
Refer to the exhibit. ![Refer to the exhibit. Based on the Enforcement Policy configuration, when a user with Role Engineer connects to the network and the posture token assigned is Unknown, which Enforcement Profile will be applied? A) RestrictedACL B) HR VLAN C) Remote Employee ACL D) [Deny Access Profile] E) EMPLOYEE_VLAN](https://d2lvgg3v3hfg70.cloudfront.net/C1454/11ec574e_f89d_329f_b2dd_79482d1aa892_C1454_00.jpg) Based on the Enforcement Policy configuration, when a user with Role Engineer connects to the network and the posture token assigned is Unknown, which Enforcement Profile will be applied?
Based on the Enforcement Policy configuration, when a user with Role Engineer connects to the network and the posture token assigned is Unknown, which Enforcement Profile will be applied?
A) RestrictedACL
B) HR VLAN
C) Remote Employee ACL
D) [Deny Access Profile]
E) EMPLOYEE_VLAN
G) None of the above
Correct Answer

verified
D
Correct Answer
verified
Showing 1 - 20 of 34
Related Exams